Government Anti-Fraud Funding for Identity Verifications

Government Anti-Fraud Funding for Identity Verifications
Recently the White House released a plan to stop the ongoing systemic fraud that many states and agencies faced these past few years. Covid allowed for an explosion in easy money through new programs that did little in due diligence. With many at home, they turned to communities working together to exploit the programs. While fraud detection systems have thwarted a lot of these groups, they remain pervasive, with them moving deeper underground. In 2023, Telegram, Discord, and Reddit groups are still going strong, but chats have diverged into further sub-groups. Similar to how governments have layers of verifications to access loan/fund reliefs, the fraud groups also add their systems to keep out monitoring. They even have built bots and techniques to counter the “rippers” and fraudsters scamming their fellow fraudsters. The same top problem states face with trusting if an applicant is truthful also applies to fraudsters. They constantly deal with lower-level fraudsters who prey on others when they outsource a service. There are usually no rules in these communities, so it turns to reputation and vouching as a way to admit more fraudsters. They sometimes have more complex verifications than what is performed by states for rent relief. In the more prominent groups, they know they are being monitored and have made new techniques more challenging to track without access to private chats.
The fraud problem is not new and has been called out by many since the beginning of the pandemic. Unfortunately, it took three years to invest in the situation, where most fraudsters have cashed out and funds transferred to untraceable methods. A few blogs and podcasts called out the issue early on but were frustrated by the lack of care for the problem. Fraud professionals were able to detect these issues early on but had little backing to stop the damage. With these new investments, there should be a change of attitude to the problem.
Articles and Podcast References
https://frankonfraud.com/fraud-trends/billions-in-fraud-went-to-dead-people-and-prisoners/
https://frankonfraud.com/wp-content/uploads/2020/10/OIG-REPORT-RELEASED.pdf
https://frankonfraud.com/fraud-trends/id-me-responds-to-claims-it-inflated-covid-fraud-losses/
https://podcasts.apple.com/us/podcast/fraudology-podcast-with-karisse-hendrick/id1530461089
Now to look at the plan, some important call-outs exist for the identity verification industry. While not all the investments will be directed towards identity-proofing tools, it is just one piece in the anti-fraud strategy.
$600m is allocated to investigating the fraud. The problem here will be most of the puppeteers are in countries that will ignore any requests for action. China, India, and Nigeria had massive operations to exploit the programs initially. Eventually, they automated certain aspects and handled the process virtually. Also, many smarter ones had multiple layers of deception to hide their trail. Listen to this Podcast on Identity Job Theft if you want a parallel to how well and hidden these programs are managed. Going after the operators is extremely important in the fight against fraud, but the reach of the law doesn’t extend well in certain countries. A supported effort by threat hunters with cyber and financial forensics experience then working in coordination is critical to tracking the sources. Easy tracking will be the people that used their real identities to withdraw the funds or shared similar bank accounts. But the network grows much more prominent when funds start moving across borders or dropped into multiple synthetic identity accounts. Hopefully, the plan will include a deep neural network algorithm to connect the hidden layers. The focus will be on the big wins up front, but eventually, the more sophisticated fraudsters will probably end up getting away with their scams.
The following compelling statement is “multi-state data to detect instances of multi-state fraud” This should have been done long ago with a basic block or review list on non-sensitive data. The dataset could have IP, Phones, Image hashes, DL #, SSN, addresses, etc. Take the same model e-commerce stores are doing with tokens to keep privacy intact. Then states can check a database to see which data matches without sharing sensitive information. States sometimes have difficulty working together and sharing their resident’s data. A common platform for sharing the data can be built at the federal level, but the states will still need the freedom to choose the data identifiers they want to match for multi-state fraud. Tools like Sift and Identiq are ways to share cases of fraud across industries and peers. The multi-state solution should also have some type of risk scoring to ensure applicants are not blatantly denied benefits. This will make identity proofing essential as high assurance should be applied to cases where a fraudster previously used a real person’s identity. Usually, when a fraudster steals one identity, they keep reusing the data across multiple states to extract all the value.
Another important statement is “Provide at least $300 million for the Pandemic Inspectors General and PRAC investigative staff” This is a massive ramp-up in staff. Most of the activities can be automated. Even initial outreach to suspected cases can give fraudsters a second look at coming clean. Many people that participated in the schemes may have a change of heart and realize their mistakes if they are questioned. A request for more information about their loans or any identifying information will be critical. Manually reaching out will cost a lot of human resources and money to complete. The staff should be using machine learning and training a system that can filter cases to a prioritized list. Run the datasets through multiple fraud tools and see which performs the best. Putting the data in Amazon Fraud Detector would probably return a significant initial caseload of fraudsters. Most of these bad actors will continue committing crimes, leaving breadcrumbs that other businesses have seen. It takes a more extensive network of companies and governments to come together to identify the worst offenders. Google, AWS, and Azure all have solutions to aid the investigation process. The largest tech platforms can be used in conjunction to map out where the fraudsters are overlapping, and then a proofing or manual remediation process can be implemented. If fraudsters are becoming technically savvy in their endeavors, then the response needs an even more complex technical identification program with oversight by the hired staff.
Another statement covers outdated verification methods “It is clear that reliance on historic knowledge-based verification (e.g., Social Security number, date of birth), is more and more susceptible to attacks” It is reassuring that the administration has realized this data is essentially worthless for protecting other program security. Many services exist where you can buy a credit report about anyone for a few dollars. Even more complex setups can be bought that are still bypassing SBA checks. Fraudsters are training each other on how to avoid knowledge-based verifications. It shouldn’t just apply to KBAs or SSNs. At this point, creating fake IDs is almost as easy as the SSN / DOB checks.
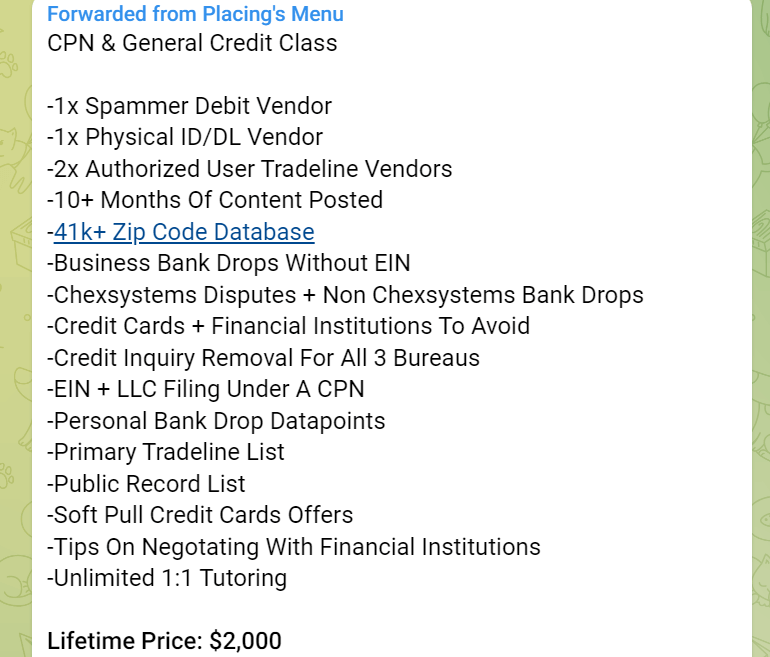
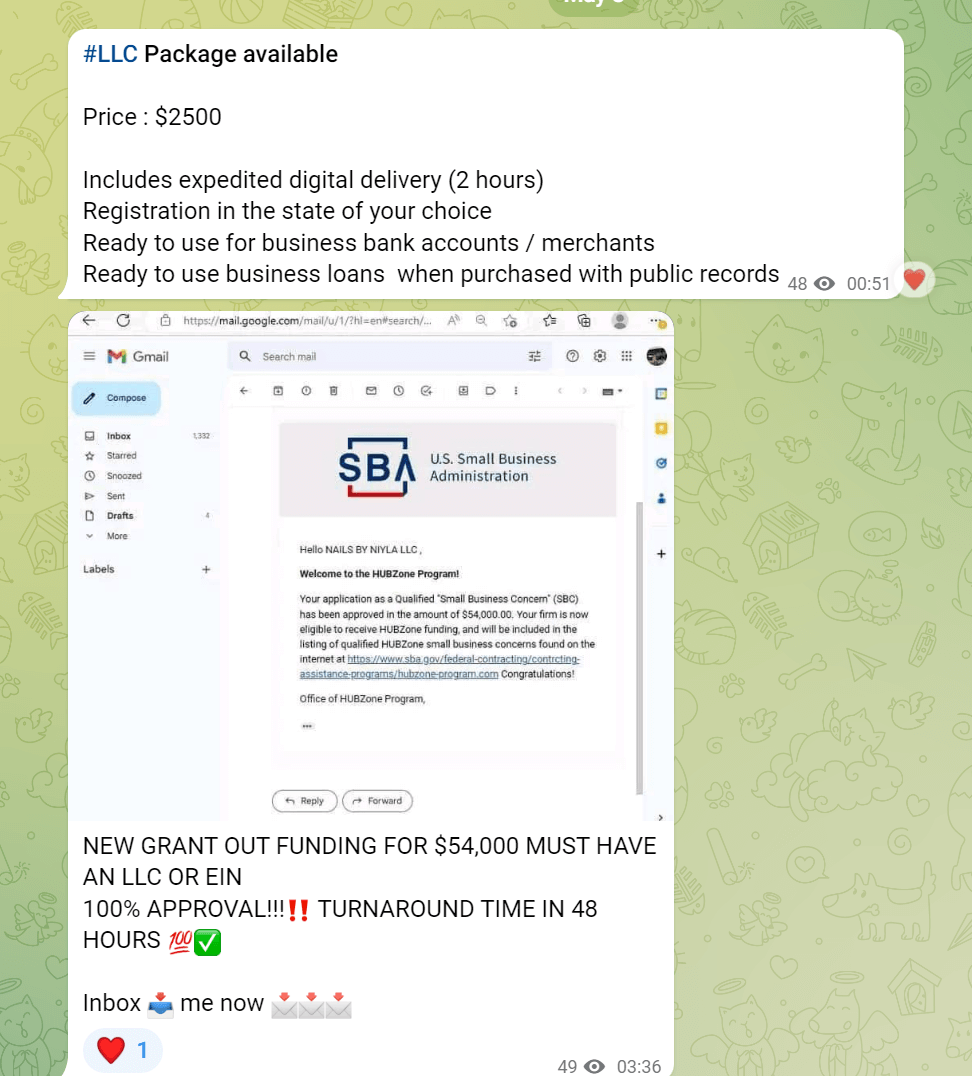
The historic verifications might not all be discarded, but it is more like a one-second toll check a person must pass through. According to the dollar amount, the system needs to be more adaptive. If you monitor the communities, you can see they have their economy with dynamic pricing depending on the value extracted from the government/taxpayers. A $2k LLC to obtain a $54k SBA grant would net a hefty return for a fraudster. The ROI keeps the fraud cycle funded as the way to stop it would be to make it uneconomical long term. Having an adaptive system that relies on multiple checks and anti-fraud strategies will make it difficult for fraudsters to resell these cookie-cutter packages.
The final exciting statement is, “This proposal would also require states to check claims against the National Directory of New Hires and prisoner datasets.” There are plenty of datasets that applicants should be checked against. Death datasets are another one that people should be checked against. They should even use datasets from enterprises such as banking, telecom, and utilities. The government needs to take a similar approach to what most businesses follow against fraud. Once these bad actors lay the seeds, they will return unless there are radical changes in the verification process. Minor changes and slow-moving updates give the bad actors time to adjust their strategies online. There is no let up on their planning for their subsequent fraud attacks, as the U.S. is still the most lucrative target to exploit. When modernizing state programs, they should be encouraged to use available solutions in the market used for fraud prevention. A layering approach is critical to immune the process to future identity thefts. The statement in the plan about a warning system is also an interesting idea. Many would expect data about citizen's or non-citizen's addresses or updated contact information to be available. The IRS would be a good starting point to have the most recent address or phone of an identity. It should then be cross-checked against other datasets, such as the DMV, to verify if there are any differences. Stopping fraud before it happens is the most effective deterrent, as it will make the entire process uneconomical. Having these new warning systems and step-up anti-fraud programs is a move in the right direction. The example mentioned in the article about fake employee fraud only took the act of notification to stop it. If there is enough messaging about an initial loan or application, then it can stop many cases. The process needs to change also from just physical letters to phone calls, SMS, or email targeting. In the end, the fraudsters have plenty of funds to invest in new workarounds and will continue looking for the easiest targets.
The new investment is a significant change in direction and may turn the tide in the coming years, depending on the ability to implement the plan. The outline provided by the White House should be enough for states to address their fraud problems seriously. The fastest and most effective way to deal with fraudsters is in life due to how quickly fraud adapts. Too much time on a strategy should not be wasted as by the time a vendor and tool are selected, and the bad actors will already have a new bypass method, as detailed in our previous articles. This agile approach is how Trust Swiftly has advanced against multiple actors by applying an array of detection and response methods for fraud. The government must take a similar system where tools are rapidly tested on real fraud cases with the best ones implemented.