Ways Fraudsters Perform Identity Theft
A 2019 Internet Security Threat Report by Symantec stated that cyber-attackers are expanding their targets and using cleverer methods to perform identity theft and scam — and nobody is exempted.
Almost 10% of individuals are now victim of identity theft every year, with 21% of these people having been victimized numerous times.
Identity theft is a big problem in the US. As reported by Javelin Strategy & Research, 13 million customers fell victim to identity scam last year and it costed them $3.5 billion in out-of-pocket expenditures.

With technology developing so quickly, impostors now have more chances than ever before to access your confidential information for their own advantage. Protecting private data can help safeguard you from falling prey to their crime.
Along with being proactive, understanding how to identify deceitful activity that’s already happened can help you avoid more harm and possibly recover your damages.
There are various kinds of identity theft and scam, including some less popular methods that could inflict chaos in your fiscal life if you don’t notice them on time. Below are a few ways fraudsters perform identity theft and tips on how to prevent them.
Account Takeover (ATO) Fraud
Account takeover occurs when someone gets access and takes control of your accounts without your awareness or consent. They use the account just as you would, possibly using it to make duplicitous transactions, transferring money, or gaining access to other accounts.
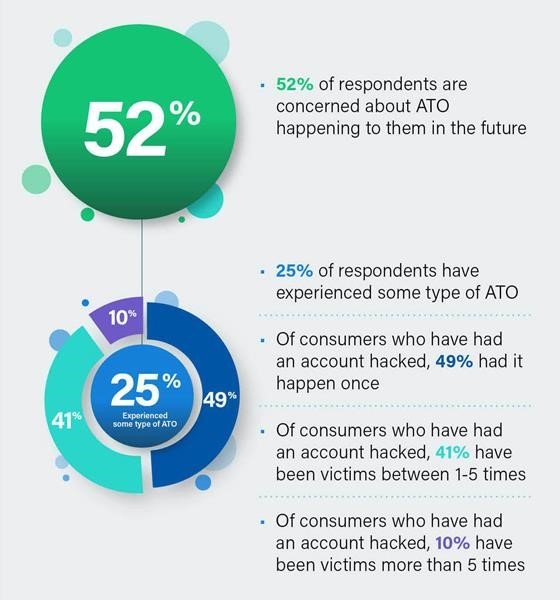
According to Sift, the leader in Digital Trust & Safety, attempted account takeover rates (the ratio of tried fake logins over total logins) increased 282% between Q2 2019 to Q2 2020.
As offenders need access to your user authorizations to get into your accounts and impersonate you online, keeping this info secure is essential. You should create strong passwords that are unique to each of your accounts. Choosing two-factor authentication and using a VPN when retrieving public Wi-Fi can add an additional level of security.
Debit/Credit Card Fraud
Debit and credit card scam happens when somebody uses your card without your consent. Although the offender doesn’t have access to your physical card, they can still use your credit card number, PIN, and security code to make illegal transactions.
They can even use your card info to try to gain access to your other accounts. This falsified activity can possibly hurt your credit in numerous ways, for instance, by disturbing your credit card balances.
Today, several card providers have implemented systems to help stop identity theft and credit card scam before it results in lasting damage. If you’re dubious about this kind of identity theft, it’s best to contact your card issuer immediately to avoid more illegal activities.

Driver’s License Identity Theft
If you ever lose your wallet, the first thing that worries you is your debit or credit card. You tend to ignore your driver’s license. However, this tiny card can be a jackpot for criminals as it mentions your physical address, driver’s license number, and other private info.
Whether your license number is embezzled in a data breach or somebody actually robs your wallet, this kind of identity holdup takes many forms.
Once somebody gets access to your driver’s license number, they could deceptively use it during a traffic stop to dodge a ticket. This means it can appear on your driving record. It is a way of identity theft that can even result in a mistaken warrant for your arrest.
In case you lose your driver’s license, report it to the cops and the Department of Motor Vehicles.
Social Security Number (SSN) Identity Theft
Your SSN can be a golden ticket for impostors, particularly if they also get access to other private info that can be used together to open fake accounts on your behalf. This can result in felonious accounts appearing on your credit reports and disturbing your credit scores. That is why it is risky to keep your Social Security card in your purse.
As an alternative, you should keep it in a secure place and shred any papers including your social security number before disposing them off.
When occasionally checking your credit accounts, check your identification info carefully. You’ll find variants of your SSN listed. Names, addresses, or other identification info you aren’t familiar with could be signs of deception.
Those who have been offended can report it to the Social Security Administration and also inform their state’s tax bureau.
Tax Identity Theft
Tax identity theft occurs when somebody uses your private info, including your SSN, to file a tax return in your name and get a reimbursement. It is typically recognized when the victim proceeds to file their tax return only to find out that one has already been administered for them.
Be wary of any message from somebody pretending as an IRS official asking for personal info. The IRS will never communicate with you in person or by phone or email without first sending notification via the mail. In case of tax identity theft, consider filling out an Identity Theft Affidavit with the IRS.
Biometric Identity Theft
This kind of identity theft involves pilfering or deceiving an individual’s physical or behavior features to tap into a gadget. For example, face or voice recognition to unlock your smartphone or to access your other devices.
It can be a treasure-trove for criminals who get access to your digital wallets and other personal info. It’s recommended to update your devices in order to safeguard yourself from this kind of identity theft. Moreover, ensure your biometric information is being kept safely by any company that asks for it.

Synthetic Identity Theft
As per McKinsey & Company, this is the most rapidly increasing type of financial delinquency in the country today. It is an advanced activity that draws on a combination of genuine private customer information, like SSN, address, and birthday, from various individuals. This data is mixed together to generate new false identities that are intended to appear like real consumers with good credit.
That’s when offenders use these fake identities to open new accounts, apply for credit, get auto loans, and perform other kinds of monetary corruptions. In case you get mails or calls inquiring about new credit accounts, or you receive mail addressed to a different name, these could be indicators of synthetic identity theft.
Internet of Things Identity (IoT) Fraud
Thanks to the latest IoT technology, everything from your phones to domestic appliances to vehicles are now synced up to the internet and linked to each other. While smart devices have made our lives easier, they have also produced a new weak spot for criminals to attack.
IoT identity fraud happens when somebody uses a security error in an internet-connected gadget to get access to your private information. As gadgets are almost always linked to significant user accounts (like your email), each gadget possibly signifies an access point for an offender.
When using IoT devices, ensure to occasionally check your monetary statements and credit reports for signs of scam. If you identify something suspicious, alter your passwords on all internet-connected gadgets right away.
Protect your house’s wireless network with a strong password and ensure all smart devices use the network you’ve configured. Alternatively, you might determine that these devices aren’t worth the risk and avoid having them in your house altogether.

Things To Do When You’re a Victim of Identity Theft
When victimized by any kind of identity theft, you should report it straightaway. Following are some other things you can do if you feel you’ve fallen prey:
File a police report. You should safeguard yourself if an identity thief starts using your info to commit crimes.
Obtain copies of the police report. You may have to show them when informing your insurer, medical providers, the credit agencies, etc.
File an identity theft complaint with the FTC. You can either contact them online or call on their toll-free number.
Ask the corporations where you know fraud happened to place a freeze or fraud alert on your credit accounts.
Close new accounts opened on your behalf and get rid of false charges from your accounts.
Depending on your situation, you may want to report a misused SSN.
Keep Customers Safe Against Identity Theft With Trust Swiftly
Being tenacious by checking your accounts and appraising your private info is the best method to stay on top of possible risks. Trust Swiftly allows you to prevent fraud before it becomes unruly by only targeting the bad users.
Dynamic friction is critical to staying ahead of your competition while avoiding impostors. With Trust Swiftly, you can detect bad guys quickly by necessitating supplementary verification. This way, you can put good users in the fast lane and increase security level, eventually creating an environment that is secure for everybody.
Using our cutting-edge solutions, you can keep synthetic identities, frauds, chargebacks, and more at bay. You can also integrate Trust Swiftly with any other fraud tool like Sift to result in the most substantial influence on fraud via automation.